The New Age of Email: Unraveling the Web of Digital Identity
In today’s era, where information is the currency, email addresses have transcended their original purpose of mere communication. They have metamorphosed into unique digital fingerprints that weave together the fabric of our online existence. This transformation, however, has not been without its pitfalls: cluttered inboxes, a loss of control, and a looming threat to privacy. The good news? There are tools and strategies available to help you reclaim your digital autonomy.
The Email Quagmire
Once, the email inbox was a sanctuary of order and tranquility. Every email had its place, and the coveted "inbox zero" was a daily achievement. Today, the landscape is vastly different. Inboxes are inundated with unsolicited messages, obscuring critical communications and overwhelming us. How did we arrive at this juncture?
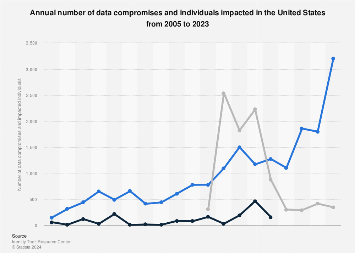
The root of the problem lies in the omnipresence of our personal email addresses. They are our digital passports, used for everything from online shopping to government interactions. This universality and the rise of data breaches and the burgeoning data brokerage industry have left our personal information exposed and ripe for exploitation.
A Strategic Response
The antidote to this digital malaise is not as complex as it may seem. You can compartmentalize different facets of your online life by employing unique email addresses and aliases. Here's a tactical approach:
- The Catch-All Strategy: You can establish a catch-all email address using a custom domain. This tactical move allows you to manage all emails sent to your domain, even those to non-existent addresses. It's a dynamic defense against spam, enabling you to filter out compromised addresses at will. Proton Mail offers a highly recommended catch-all email address option.
- The Alias Maneuver: Hide My Email is a service by Apple that lets you keep your personal email address private whether you're creating a new account with an app, signing up for a newsletter online, or sending an email to someone you don't know well.
Alternatively, Simple Login is an open-source email alias solution that acts as a forwarding service, providing permanent aliases that shield your actual email address. It's a strategic layer of privacy and control.
The Strategic Advantages
- Commanding the Spam Battlefield: Unique email addresses empower you to filter or entirely shut down compromised addresses, giving you control over the spam siege.
- Fortifying Against Identity Invasion: By dispersing your digital identity across unique email addresses, you build a robust defense against cyber criminals.
- Monitoring the Data Trade: Unique addresses enable you to track which entities are trading your information, giving you intel on your digital footprint.
The Tactical Considerations
These solutions, while potent, are not without their complexities. Some say online platforms may resist certain email alias domains, and a single domain strategy may still reveal connections between addresses. However, these are mere skirmishes in the broader battle for control.
WTF?
In a world where personal information is traded like stocks, mastering our email environment is not just a luxury; it's a critical mission. The time has come to strategize, take command, and restore our inboxes to their former glory.
Using unique email addresses and aliases helps maintain email hygiene and digital privacy. Whether through catch-all strategies or services like Hide My Email / Simple Login, these tools are not mere conveniences but essential instruments in our modern times.
The information age has ushered in a complex web of digital connections, transforming our once-simple email addresses into a labyrinth of potential exploitation. But with the proper arsenal of tools and a strategic understanding of the landscape, control can be reclaimed.



Member discussion